| Nuclear Facilities and Cyber Attack – New Weapons, Old Techniques |
 |
|
By Samuel Bocetta
Tuesday, November 14 2017 |
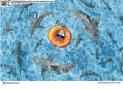
Last month, a wave of cyber attacks hit Ukraine and neighboring nations. The most visible outcome of these attacks, and by far the most widely reported, were on the Russia’s largest news agency, Interfax, and Odessa airport. The attacks, though quickly fixed, caused disruption for both organizations. Less well reported was that the attacks also targeted the retired Chernobyl nuclear reactors. The malware used, named “BadRabbit," was able to infiltrate the radiation monitoring systems in use at the Chernobyl site. Chernobyl is no longer a functioning nuclear reactor, of course, but the fact that it has been the victim of several attacks in recent months, including the Petya worm back in June, which was able to completely shut down its monitoring systems, and force engineers back to manual monitoring systems, has raised questions about its security. The problem is not limited to Ukraine and Russia. A report issued in July by the Department of Homeland Security and the FBI said that since at least May 2017, hackers had attempted to penetrate the computers of companies that run nuclear plants in the U.S., including the Wolf Creek Nuclear Operating Corporation, which runs a nuclear plant near Burlington, Kansas. There are currently 61 commercially operated nuclear power plants in the U.S., incorporating 99 reactors, located in 30 states, according to the US Energy Information Administration. No “operations systems” were breached in the attacks, which targeted corporate intranets, and seemed designed to steal financial and administrative data rather than cause direct disruption. In a joint statement with the F.B.I., a spokesman for the Department of Homeland Security said, “There is no indication of a threat to public safety, as any potential impact appears to be limited to administrative and business networks.” Protecting Nuclear Facilities In a sense, that is not surprising. Nuclear facilities are among the most hardened sites in the U.S., and with good reason. They are kept separate from the wider internet, and there are rigorous restrictions on employees carrying hardware and data in and out of such plants. The model used for protecting nuclear facilities today owes much to the lessons of the Stuxnet virus. This was a computer worm that surfaced in 2010, when technicians working at the Natanz uranium enrichment plant in Iran reported that their centrifuges were failing at a hugely increased rate. The virus was designed to spread across the internet, like more recent worms, but the payload was specifically targeted to only become active when it had infected the control computers for Iranian centrifuges. Though the weapon has been widely regarded as a U.S./Israeli creation, the two governments continue to deny involvement. The heart of security protocols at U.S. nuclear plants is the implementation of an “air gap." In practice, this means a physical separation between the systems in use at the plant, and external computer networks. Of course, nuclear plants cannot be entirely isolated, because they need to send monitoring data to other facilities. To do so, they make use of data diodes – hardware devices that allow data to pass in one direction only. In addition, the operational software and hardware of nuclear plants sit behind multiple levels of protection. “United States utilities with nuclear assets have very robust cyber security programs dating back to the days of Y2K,” David Blee, executive director of the National Nuclear Infrastructure Council, told Forbes. “Operational plant systems controls are segregated from normal business software by several layers of protection, including physical means.” Nuclear plants are required to report any breaches to the Nuclear Energy Institute, and so far none have done so. The New Normal This might sound reassuring. However, in order to fully assess the vulnerability of nuclear facilities to cyber attack, the broader geopolitical environment also needs to be strenuously examined. There is a paradox at the heart of recent cyber attacks. They are based on worms that exploit vulnerabilities in operating systems, can spread extremely rapidly across the internet, and often use tools stolen from the NSA. Yet, recent worms have carried a rather strange payload. For instance, the WannaCry virus, recently confirmed to have originated in North Korea, carried ransomware normally associated with criminal hackers out to make a quick buck. It was able to access files on victims’ computers, and to extort money for their return, but such pedestrian criminal intent can hardly be a motivation for a state cyberespionage actor. It’s this anomaly that has led to the widespread conclusion that recent attacks are no more than “weapon tests," of a kind we have not seen since the end of the Cold War. The current conclusion is that WannaCry, BadRabbit, et al, represent Russia and the DPRK testing techniques that will eventually be used in more sophisticated and targeted cyber weapons. Indeed, the Cold War analogy might be the best one through which to understand the current state of cyber warfare. Just last week, several news sources reported that Russian hackers were targeting a cyber security conference in D.C., using a macro hidden in a flyer, in order to collect intelligence from attendees, and ultimately select specific individuals to spy on. New Weapons, Old Techniques There is something of a blindness when it comes to the vulnerability of nuclear plants. They are hardened against external infection, but no system is invulnerable to determined sabotage, particularly from within. Not to be alarmist, but high-profile defectors like Edward Snowden, who exposed reams of classified NSA data, show that protecting nuclear facilities from cyber attack should be based on far more than hardening systems. A determined saboteur, especially one willing to be imprisoned for his or her acts, could easily infect such systems. Motivation need not be driven by some ideological belief, of course. To return to my initial point, the fact that the recent attacks on Wolf Creek were “only” able to access corporate and personal information makes them sound much less dangerous than they are. Personal information, in particular, can be used to blackmail employees into releasing cyber weapons in the facilities in which they work. In short, then, we need to move away from a technical paradigm, and toward one that acknowledges the human complexities of the latent conflict we now confront. The ultimate defense of nuclear plants in the U.S. may well rely less on high-tech wizardry, and more on protecting employees from blackmail and extortion. On a broader level, policymakers need to recall a view of security that may have been lost since the end of the Cold War: International politics is an ideological realm, and attacks are characterized as much by ideology as technical capabilities. The fact that the Shamoon virus, responsible for recent attacks on oil facilities in Saudi Arabia, contained a picture of a burning American flag, should prove that much. This realization, once accepted, suggests that some of the best ways to protect U.S. nuclear plants from cyber attack are the oldest: vetting of employees, and strong intelligence on the sympathies and capabilities of our potential enemies. Samuel Bocetta is a freelance journalist specializing in U.S. diplomacy and national security, with emphases on technology trends in cyberwarfare, cyberdefense, and cryptography. He spent decades working for the U.S. Navy and consulting for defense contractors, specializing in electronic warfare and advanced computer systems. He currently writes for Gun News Daily and teaches electrical engineering part time. |
Related Articles : |