| A Layman's Guide to Bot Wars |
 |
|
By Samuel Bocetta
Monday, March 12 2018 |
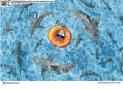
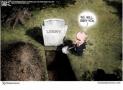
Cyberwarfare. It's a term we hear more and more these days, but most of us don't really know what to make of it. Cyber meddling was thrust back into the news once again this February. Special Counsel Robert Mueller's indictments against 13 Russian nationals accused of attempting to manipulate public political opinion before and during the 2016 presidential election made cyberwarfare a hot topic. Even so, that effort was only propagandistic and fairly limited in scope and impact. Cyberwarfare sounds more than a little confusing at first glance. That's because bot activity is a complicated matter, one with a ton of moving parts. Bots themselves, which are simply automated software applications executing simple commands, come in myriad forms, some good, some bad, but all are intended to provide speed and volume across the internet far beyond human capability. For the sake of simplification, I've done a deep dive on the subject to help you unpack this troubling subject. No doubt, you have tons of questions, such as, “What is cyberwarfare?,” “How does it work?,” and “Can it be traced to its origin?” I'll cover all of this and more in the following guide. Strap in and get ready to be surprised at the staggering stats on this growing phenomenon. What is Cyberwarfare? In the simplest of terms, cyberwarfare is a sequence of digital attacks intended to disrupt or damage networks or computer systems in a rival nation state. You may have heard the word “cyberwarfare” in reference to ransomware or other malicious software programs. Cyberwarfare consists of hacking networks to conduct attacks on a target's strategic or tactical resources for the purpose of sabotage or espionage. This includes anything that assists a country in expressing its political will or or waging war. Targets may include military facilities, weapons, fuel for jets and planes or any combat elements used to achieve combat objectives. While it is true that a nation state may use ransomware on their enemies, the vast majority of ransomware attacks are perpetrated by criminal hackers. These are cyber attacks which, technically, do not qualify as cyberwarfare, although an argument can be made that both are of a piece, as the expectation is the same in both case: the intention to terrorize or harm those targeted. State-backed hackers seek to disrupt civilian and military services and potentially create real-world effects. This can affect anyone who is reliant upon digital infrastructure. What Does it Look Like? Governments around the world have been dumping billions of dollars into cyber defense and cyberwar research to ensure that they can fight the internet battles of today and those threat trends that are on the horizon. In the U.S., President Trump has signed a $700 billion military spending bill which enacts several cybersecurity measures. At the same time, Trump's objection to certain cyberwarfare-related language in the bill illustrates what a baffling and tenuous subject cyberwarfare is. Future wars are expected to be fought not only with traditional military might but with the aid of experienced hackers who are adept at utilizing computer coding to attack the infrastructure of our enemies. The largest concern among government officials and intelligence agencies is that cyber attacks could affect vital infrastructure like power grids or banking systems. It was previously believed that no hacker would be sophisticated enough to pull off an attack on the power grid, but this has since changed. In September of 2017, security firm Symantec alerted the media to a rash of hacker attacks that compromised energy companies in the US and abroad. In a handful of these cases, Symantec said that the hackers had gained “call operational access." Call operational access refers to control of the interfaces power company engineers rely on to send commands to equipment like circuit breakers, enabling them to stop the flow of electricity into homes and businesses. How it Works & Why We Should Be Alarmed If it's not obvious by now, cyberwarfare can do some serious damage to critical infrastructure, the kind of damage that could leave Americans without power. Perhaps the scariest thing about a cyber attack is that it can be launched instantaneously from anywhere in the world. Whereas traditional military attacks are often able to be foreseen, there is rarely any evidence of a cyber attack during the build-up. Nation states can carry out these attacks the same way one would hack any computer or system. They learn all that they can about the target's system, assess its weaknesses and exploit those weak spots to gain purchase and/or destroy said system. So why should we be concerned? Well, there were 480 million more internet users in 2017 than in 2016, bringing the global tally up to 3.74 billion users. That's a lot of people exposed to a lot of threats, whether it's government meddling and malware, WannaCry-style ransomware or just anyone with the capacity and interest in collecting and sharing our data with third parties or using it for their own purposes. The Equifax credit service security breach alone impacted the personal data (up to and including social security numbers) of almost 150 million Americans. Because those numbers are so staggering, particularly when combined with other similar massive efforts, how and by whom the information is being used, if it is being used, is curently unknown. Can a Cyberwarfare Attack Be Traced? Tracing an act of cyberwarfare back to its origins is extremely difficult. One common practice that attackers employ to elude detection is to break into poorly secured computers and use the hijacked systems as proxies through which they can launch and route global attacks. To trace an attack, a profile must be built by identifying the group responsible. To determine the origin of the attack, one must determine the origin of the machines that operate as command and control. In many cases, this involves creating a “digital fingerprint” of the hackers and using it to distinguish one “threat group” from others. In other words, you look at several incidents of cyber attacks and study the methods and tools used in the attack to detect a pattern. Those who investigate cyber attacks pay attention to what information hackers choose to steal and the care with which they disarm alarms or remove any evidence. This assists in ascertaining how sophisticated the hackers are, which can help to determine where the attack is likely to have come from. Those who build such profiles take all factors into consideration, since reliance upon isolated evidence is generally insufficient in figuring out who was behind the attack and how to prevent such attacks in the future. How to Tell the Difference Between an Actor & a Prankster Maybe you remember that time a teenager hacked into the Pentagon's websites and brought six "bugs" to the attention of the US Defense Department. That's what we call a “white hat hacker,” someone who breaks into a computer system in order to help the people who own the system. While there are many white hat hackers out there, the overwhelming number of hackers are black hat hackers with criminal intent. Of course, all cyber attacks should be taken seriously, but for those who are navigating the murky waters of cyberwarfare, a distinction needs to be made among pranksters, criminal elements and nation state threat actors. A standard hacker is someone who uses their technical knowledge to overcome a problem. The word “hacker” has become synonymous with criminal activity, but it actually refers to any computer programmer. The word has become pop culture shorthand for “security hacker” because hackers exploit bugs to break into computer systems. Threat actors differ from other hackers in that they are directly and deliberately responsible for a security incident which impacts an organization's security protection and sensitive data. A threat actor doesn't necessarily have the same set of skills as a hacker. The threat actor's mission is to compromise an organization's security. The aim could be to copy sensitive information or physically demolish that information. Non-state actors are sometimes recruited for cyberspace operations. Employment of such non-state actors as so-called patriot hackers or cyber-militants is not uncommon. When Does it Happen & Who is Responsible? It appears to be happening more and more. More than 140 countries have a cyber weapons development program. Russia's cyberwar on Ukraine has rung more than a few bells with security experts and has been called a blueprint for what's to come. But Russia is hardly alone in its malicious attacks on neighboring nation states. China's cyber-spies have been hacking countries left and right. They were blamed for the enormous data breach at the US Office of Personnel Management that compromised the data of more than 21 million people. In May of 2014, U.S. federal prosecutors indicted members of the People's Liberation Army for cyber-espionage for economic gain. Their cyber operations are believed to be an active threat by experts in the field. The 2015 attack on GitHub illustrated the increasing expertise and aggression of China's cyber-spies. In November of 2010, a group calling themselves the Indian Cyber Army hacked websites belonging to the Pakistan Army, the Ministry of Foreign Affairs and more as an act of revenge for the Mumbai terrorist attacks. In response, a group calling itself the Pakistan Cyber Army retaliated by hacking the website of India's Central Bureau of Investigation. One year earlier, coordinated denial of service attacks against government, media and financial websites in South Korea were traced back to the United Kingdom. In 2012, seven Iranian nationals were indicted for installing malicious code on a computer that controls a dam in New York State. This begs the question: Who is prepared to combat this mushrooming cyber problem? Forbes has said that Israel leads the world in cyber/technology innovation and it's clear to see why. Israel has military conscription, a highly specialized cyber-intelligence operation within their military and an ever-growing number of innovative cyber-startups. The UK's Government Communications Headquarters has more than doubled its offensive cyberwarfare ability, not surprising given the fact that British Army Chief Nick Carter has called cyberwarfare a “greater threat than terrorism." What Can We Do? There are many security solutions for protecting one's privacy and preventing malicious attacks from occurring. These include free software programs and mobile apps as well as premium subscription services. If we're talking about a potential threat actor, there are privileged access management solutions that manage privileges, log all activity in the form of session recordings or keystroke logging, and monitor applications to make sure that a threat actor cannot gain access. Legal scholars have spent years working to explain how international law can be applied to digital warfare. Their efforts have formed the basis of the Tallinn Manual, a comprehensive academic analysis of how extant global laws apply to cyberspace. For those who want to surf the web or communicate with the outside world without running the risk of being tracked or attacked, VPNs (virtual private networks) are a cheap and easy tool for concealing one's IP address, securing one's activity and preventing data leakage. In an age where more and more people are investing in digital assets, there is a danger of having one's funds hijacked by cybercriminals. Hackers have held local government websites hostage, demanding a ransom be paid in Bitcoin. For those charged with overseeing government facilities and public works, redundant manual processes can make a big difference when it comes to recovering operations in a timely manner. After a cyber attack on Ukrainian power stations in 2015, employees were able to recover in under seven hours because of redundant manual processes. Innovation will be key to thwarting cyberwarfare, but the government sector is notoriously slow in obtaining information and communication technology. This will have to change if America and its allies are to ward off state actors and black hat hackers. System-level policies should exist for probable cyberwarfare targets and security frameworks should be put in place. Risk management is also a key factor in determining a reasonable and appropriate defense. Facilities should maintain monitoring, security protocols and incident response. Closing Thoughts There are many threats facing us today and there is, perhaps, none greater than that posed by cyberwarfare. But cyberdefense exercises like the NATO-backed Locked Shields event send a strong message of assurance. Although cyberwar is a harsh reality, it won't lead to a digital apocalypse. Samuel Bocetta is a freelance journalist specializing in U.S. diplomacy and national security, with emphases on technology trends in cyberwarfare, cyberdefense, and cryptography. He spent decades working for the U.S. Navy and consulting for defense contractors, specializing in electronic warfare and advanced computer systems. He currently writes for Gun News Daily and teaches electrical engineering part time. |
Related Articles : |